Let’s Encrypt (LE) is a certificate authority that issues free SSL certificates for use in your web applications. This post details how to get LE setup to support Cloud Director specifically with a wildcard certificate.
Certbot
LE uses an application called certbot to request, automatically download and renew certificates. You can think of certbot as the client for LE.
First you’ll need to create a client machine that can request certificates from LE. I started with a simple CentOS VM. For more details about installing certbot into your preferred OS read this page here.
Once you get yours on the network with outbound internet access, you can start by performing the following.
# Update software
yum update
# Install wget if not already installed
yum install wget
# Download the certbot application.
wget https://dl.eff.org/certbot-auto
# Move certbot into a local application directory
sudo mv certbot-auto /usr/local/bin/certbot-auto
# Set ownership to root
sudo chown root /usr/local/bin/certbot-auto
# Change permisssions for certbot
sudo chmod 0755 /usr/local/bin/certbot-autoNow you’re ready to request certificates. Run the following command but of course replacing your desired domain within the ‘your.domain.here ‘.
/usr/local/bin/certbot-auto --config-dir $HOME/.certbot --work-dir $HOME/.certbot/work --logs-dir $HOME/.certbot/logs certonly --manual --preferred-challenges=dns -d '*.vmwire.com'This will create a request for a wildcard certificate for *.vmwire.com.
You’ll then be asked to create a new DNS TXT record on your public DNS server for the domain that you are requesting to validate that you can manage that domain. Here’s what mine looks like for the above.
This means that you can only request public certificates with LE, private certificates are not supported.

You will then see a response from LE such as the following:
IMPORTANT NOTES:
- Congratulations! Your certificate and chain have been saved at:
/root/.certbot/live/vmwire.com/fullchain.pem
Your key file has been saved at:
/root/.certbot/live/vmwire.com/privkey.pem
Your cert will expire on 2020-12-24. To obtain a new or tweaked
version of this certificate in the future, simply run certbot-auto
again. To non-interactively renew *all* of your certificates, run
"certbot-auto renew"Updating Cloud Director certificates
Before you can use new certificate, you need to perform some operations with the JAVA Keytool to import the pem formatted certificates into the certificates.ks file that Cloud Director uses.
The issued certificate is available in the directory
/root/.certbot/live/Navigate to there using an SSH client and you’ll see a structure like this

Download the entire folder for the next steps. Within the folder you’ll see the following files
| Filename | Purpose |
| cert.pem | your certificate in pem format |
| chain.pem | the Let’s Encrypt root CA certificate in pem format |
| fullchain.pem | your wildcard certificate AND the LE root CA certificate in pem format |
| privkey.pem | the private key for your certificate (without passphrase) |
We need to rename the file to something that the JAVA Keytool can work with. I renamed mine to the following:
| Original filename | New Filename |
| cert.pem | vmwire-com.crt |
| chain.pem | vmwire-com-ca.crt |
| fullchain.pem | not needed |
| privkey.pem | vmwire-com.key |
Copy the three new files to one of the Cloud Director cells, use the /tmp directory.
Now launch an SSH session to one of the Cloud Director cells and perform the following.
# Import the certificate and the private key into a new pfx format certificate
openssl pkcs12 -export -out /tmp/vmwire-com.pfx -inkey /tmp/vmwire-com.key -in /tmp/vmwire-com.crt
# Create a new certificates.ks file and import the pfx formatted certificate
/opt/vmware/vcloud-director/jre/bin/keytool -keystore /tmp/certificates.ks -storepass Vmware1! -keypass Vmware1! -storetype JCEKS -importkeystore -srckeystore /tmp/vmwire-com.pfx -srcstorepass Vmware1!
# Change the alias for the first entry to be http
/opt/vmware/vcloud-director/jre/bin/keytool -keystore /tmp/certificates.ks -storetype JCEKS -changealias -alias 1 -destalias http -storepass Vmware1!
# Import the certificate again, this time creating alias 1 again (we will use the same wildcard certifiate for the consoleproxy)
/opt/vmware/vcloud-director/jre/bin/keytool -keystore /tmp/certificates.ks -storepass Vmware1! -keypass Vmware1! -storetype JCEKS -importkeystore -srckeystore /tmp/vmwire-com.pfx -srcstorepass Vmware1!
# Change the alias for the first entry to be consoleproxy
/opt/vmware/vcloud-director/jre/bin/keytool -keystore /tmp/certificates.ks -storetype JCEKS -changealias -alias 1 -destalias consoleproxy -storepass Vmware1!
# Import the root certificate into the certificates.ks file
/opt/vmware/vcloud-director/jre/bin/keytool -importcert -alias root -file /tmp/vmwire-com-ca.crt -storetype JCEKS -keystore /tmp/certificates.ks -storepass Vmware1!
# List all the entries, you should now see three, http, consoleproxy and root
/opt/vmware/vcloud-director/jre/bin/keytool -list -keystore /tmp/certificates.ks -storetype JCEKS -storepass Vmware1!
# Stop the Cloud Director service on all cells
service vmware-vcd stop
# Make a backup of the current certificate
mv /opt/vmware/vcloud-director/certificates.ks /opt/vmware/vcloud-director/certificates.ks.old
# Copy the new certificate to the Cloud Director directory
cp /tmp/certificates.ks /opt/vmware/vcloud-director/
# List all the entries, you should now see three, http, consoleproxy and root
/opt/vmware/vcloud-director/jre/bin/keytool -list -keystore /opt/vmware/vcloud-director/certificates.ks -storetype JCEKS -storepass Vmware1!
# Reconfigure the Cloud Director application to use the new certificate
/opt/vmware/vcloud-director/bin/configure
# Start the Cloud Director application
service vmware-vcd start
# Monitor startup logs
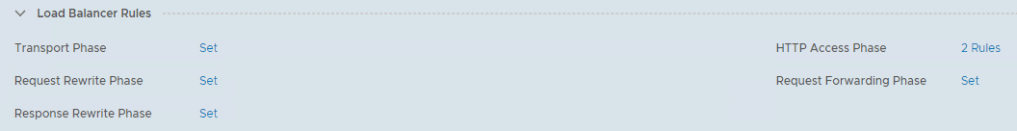
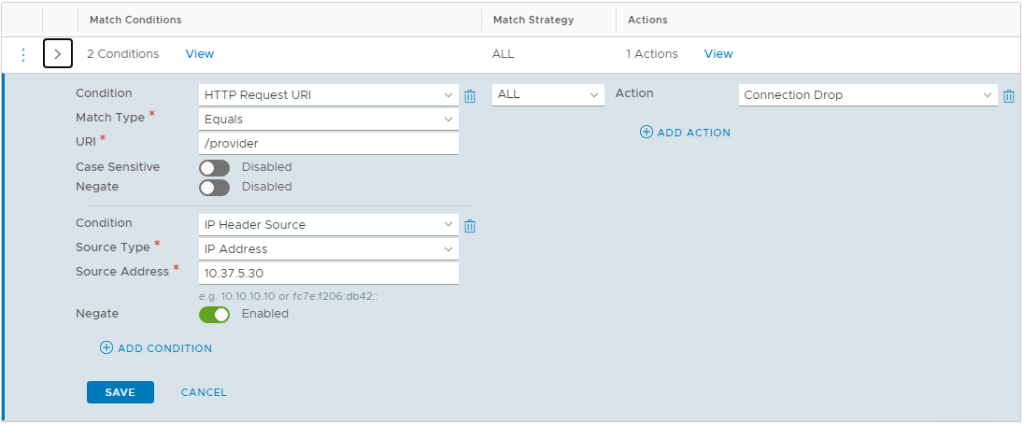
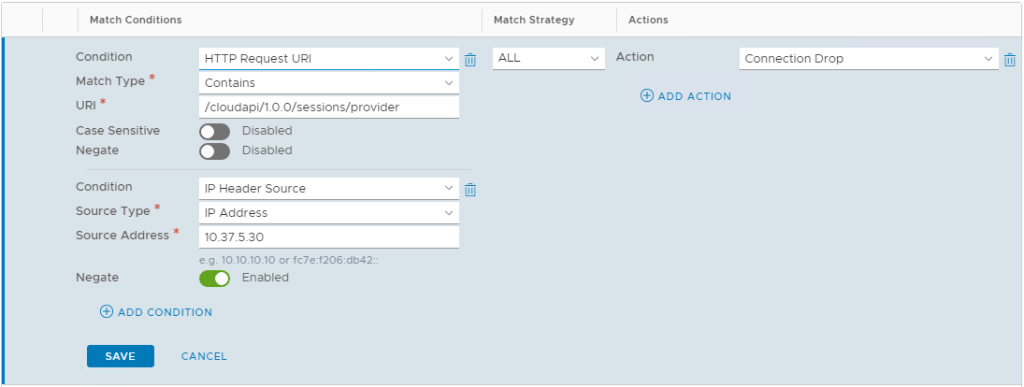
tail -f /opt/vmware/vcloud-director/logs/cell.logCopy the certificates.ks file to the other cells and perform the configure on the other cells to update the certificates for all cells. Don’t forget to update the certificate on the load balancer too. This other post shows how to do it with the NSX-T load balancer.
Check out the new certificate at https://vcloud.vmwire.com/tenant/vmwire.